Google Plugs Serious Nexus 6/6P Vulnerability; More Prone To Hackers Than iOS; Android Nougat Update Automatically Taps Security Patch
ByGoogle Nexus 6 and 6P users are alerted to secure the usage of their phone when a serious Android vulnerability has been detected. The exploit posts threats like spying in forms like eavesdropping in a phone call, automatically resend messages or divert mobile data packets.
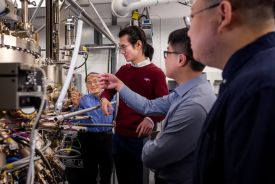
According to Ars Technica, this android vulnerability originated from the phones bootmode. Bootmode is taking advantage of a malware-infected PCs and malevolent power chargers to contact hidden USB outlets. It has been detected by security researchers at IBM's X-Force which traces relation from the flawed security cluster, CVE-2016-8467.
Google plugs security patches to prevent android vulnerabilities leak out in public. The first one has been out since November to address Nexus 6. The second wave of the update comes this January for Nexus 6P. Those who have already updated their Androids to Nougat has to worry less because it should automatically install the security patch once it becomes available.
Android VS iOS Vulnerabilities
Android disappoints upon ranking atop the 50 most vulnerable operating systems. Android has topped the list with a staggering 523 flaws. This makes Android-powered devices has more possibilities getting hacked. Meanwhile, its archrival iOS also ranked 15th but with only 161 recorded issues, according to Phone Arena. This result is the exact opposite of 2015 results where iOS ranked second with 287 flaws versus Android's 125.
The results of this OS vulnerability rankings are compiled by CVE Details. Nota Bene, OS vulnerability is a flaw or error found within the operating system which hackers can take advantage. Having aces to such vulnerability, they can make devices stuff they are not supposed to do like release private information synced in Apps or allow access to call log, contacts, IMEI numbers, SMS or even passwords saved and synced devices.
What is your thought about Android's Vulnerability? Tell your suggestions in the comment section below.
© 2026 University Herald, All rights reserved. Do not reproduce without permission.